Last week I wanted to try the GitHub container registry as an alternative for Azure Container Registry. Since many things are moving towards GitHub this seemed a good idea.
The plan I wanted to execute was as follows:
* Build a Docker Container with GitHub Actions
* Push a Docker Container to the GitHub Container Registry
* Pull the Container Locally
* Pull the container on Azure Kubernetes Service (AKS)
So this is what I did, and the steps I followed are documented below.
Build and Push a Docker Container with GitHub Actions
This was quite easy. First I created this repository where I created a very simple Dockerfile (Based on this awesome repo https://github.com/DockerDemos/FullScreenMario). After that I added a GitHub action workflow that builds and pushes this to the GitHub registry.
When navigating to the Actions tab on the repo, you can select the starter workflow “Publish Docker Container”, to get you started.
When you choose to set up this workflow, the first thing you need to do is change the IMAGE_NAME . After that you are almost done, except that you need to take notice of the following section.
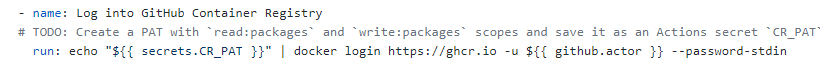
Because the GitHub Container Registry is still in Beta, you cannot use the standard Github Secrets yet. To access the GitHub Container Registry you need to create a Personal Access Token with permissions to push and pull packages and then add this as a secret to your repository.
To create a Personal Access Token, navigate to your profile settings and create one in the Developer Settings section. Follow this guide on Github Docs to create a PAT. Make sure you check the write:packages, read:packages and delete:packages permission.
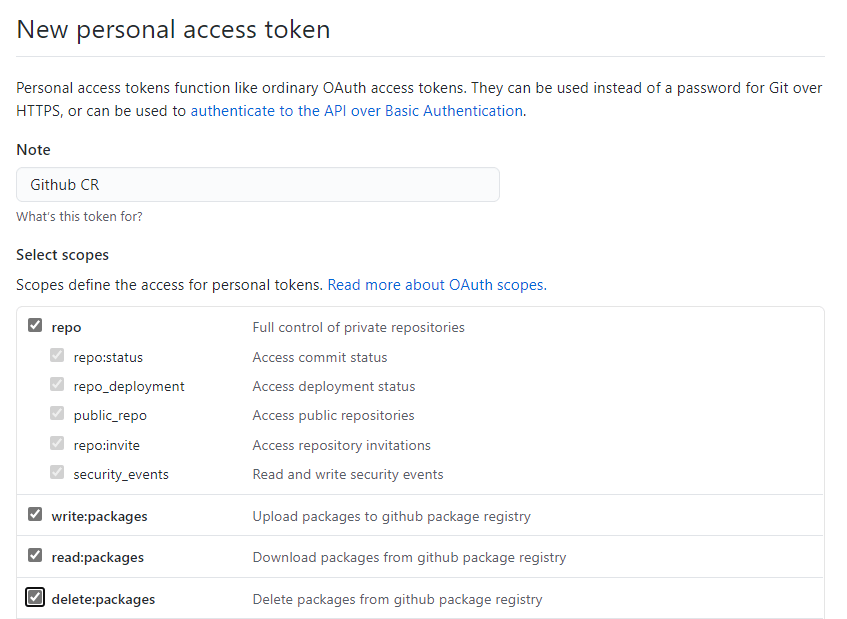
Once you created the PAT, make sure you save it on your clipboard. Navigate to your repository settings, and add a secret called CR_PAT and add the PAT you saved on the clipboard.

Back in your GitHub Actions, you can now start the Action to build and push the container.
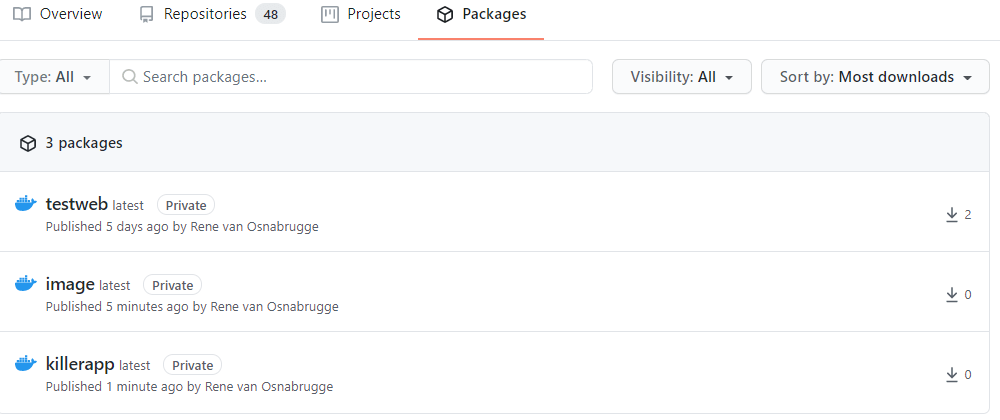
When your build completed succesfully, you can navigate to the packages section of your account, to see the Docker image. E.g. https://github.com/renevanosnabrugge?tab=packages
Pull the Container Locally
Great! We managed to push a container to Github Container Registry. Now we need to use the image. Locally it works quite simple. You need to login to the Github Container Registry with the same PAT as you created in the Github Secrets. Then execute the command below and you are good to go.
echo <YOUR_PAT> | docker login ghcr.io -u USERNAME --password-stdin
docker pull ghcr.io/<your_repository>/<your_imagename>
Look at this link for more details on this
Configure AKS to use GitHub Container Registry
Azure Kubernetes Service (AKS) works with all Container Registries that follow the Docker registry interface. So, it also work with Github. Assuming that you already have a AKS running, you need to add a Pull Secret for the Github Container Registry.
From the command line you can execute the following command
kubectl create secret docker-registry pullsecret --docker-server=https://ghcr.io/ --docker-username=notneeded--docker-password=<YOUR_GHCR_PAT>With that you add a secret to the AKS cluster. In your deployment, you need to refer to this pullsecret to get the containers. Look at the example killerapp.deploy.yml and killerapp.service.yml files in my Git repository.
When you run kubectl apply -f killerapp-deploy.yml the pod will be deployed pulling the image from the Github Container Registry!
Hope this helps!



